THE CHALLENGE
The growing danger of Advanced Persistent Threats (APTs), stealthy, multi-stage cyberattacks, poses a major challenge to detect subtle malicious behaviors hidden within massive volumes of system audit logs without overwhelming their infrastructure. Traditional defenses rely on constructing detailed provenance graphs to trace system activity, but these approaches are too slow and resource-intensive to keep up with real-time demands. At the same time, simpler anomaly detection tools often generate too many false alarms or require extensive tuning and training data, making them impractical for large, dynamic enterprise environments. As log data grows exponentially, companies face an urgent need for scalable, cost-effective, and accurate detection solutions that can quickly pinpoint suspicious activity windows without the burden of high memory usage, manual oversight, or expensive infrastructure upgrades.
OUR SOLUTION
Madeline offers a breakthrough in detecting stealthy cyber threats like Advanced Persistent Threats (APTs) by eliminating the need for complex and resource-heavy graph analysis. Instead of building costly provenance graphs, Madeline analyzes system audit logs in real time by transforming them into compact summaries of system behavior over fixed time windows. The program uses advanced yet lightweight machine learning—specifically, an LSTM autoencoder—to learn patterns of normal activity and flag unusual behavior as potential threats. To reduce false alarms, Madeline applies a smart filtering method that considers the context of neighboring time windows. This approach dramatically cuts memory and processing demands while maintaining high accuracy and low false positives. Designed for scalability and transparency, Madeline enables continuous threat monitoring across enterprise and cloud systems, making advanced threat detection more efficient, affordable, and actionable for businesses.
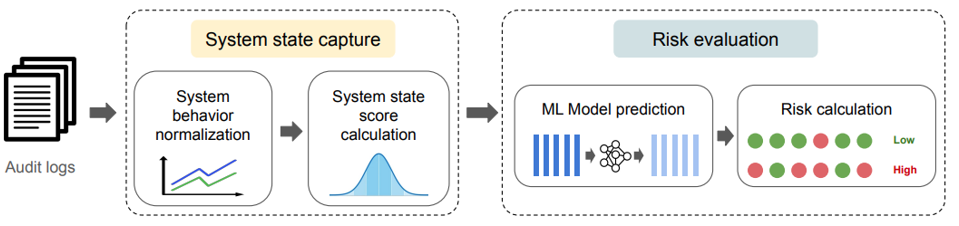
Figure: Overview of Madeline
Advantages:
- 1000× Faster processing than graph-based systems
- 5.2× Lower memory usage for efficient large-scale deployment
- High accuracy with up to 99.6% recall and only 1.1%–3% false positives
- Unsupervised & Explainable with no need for labeled attack data
Potential Application:
- Real-Time Enterprise and Government Threat Detection
- Cloud Infrastructure and Container Security Monitoring
- IoT and Edge Device Anomaly Detection
- Security Operations and MSSP Integration